Category: Programming
-

Voice-controlled blinds with Amazon Echo
For Christmas, I bought my Dad an Amazon Echo Dot. Its listening capabilities really impressed me, and it got me thinking about what features it offered to developers. After looking into the Alexa Skills API, and seeing how easy it was to get started, I decided I just had to buy one for myself. But I needed…
-
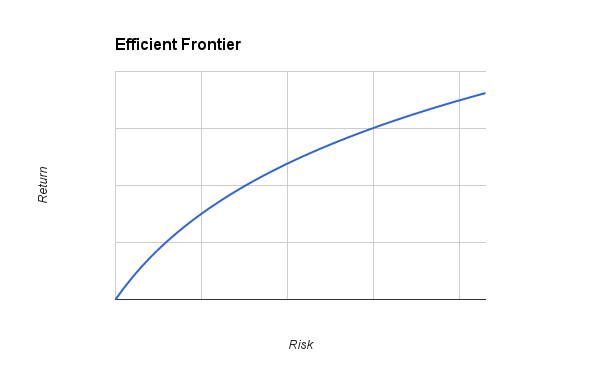
Computational Finance – Portfolio Optimization
I’ve been studying a Computational Finance module for the past few months now, and it’s absolutely fascinating. This blog post focuses on Markowitz Portfolio Optimization (AKA Modern portfolio theory), and will be part of a number of Computational Finance posts I’ll be posting over the coming months. The following post includes MATLAB examples, but these could be…
-

Drive My Internet-Controlled Car!
Radio controlled toy cars don’t normally have a Raspberry Pi, 10 batteries and a stripboard loosely hanging off them, but this isn’t your standard RC car. The primary goal of ICC was to enable a toy car (which has now become a robot, as seen in the image above) to be controlled in real-time over…
-
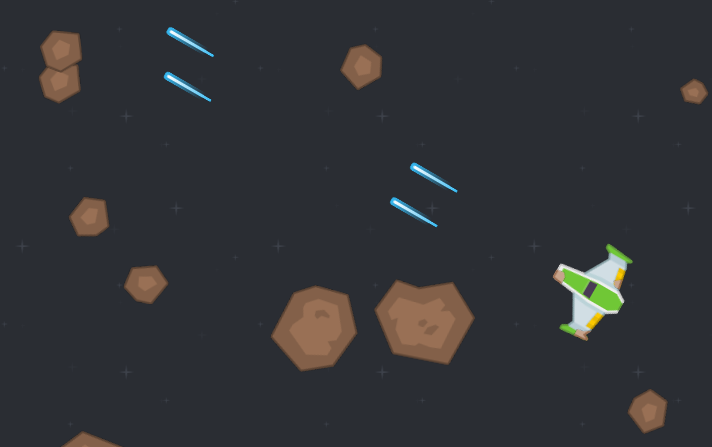
Astrovoids – Singleplayer/Multiplayer Asteroids Clone
This is a project I worked on around June 2014. It’s written in JavaScript, and uses the IvanK graphics library. The nice artwork isn’t my own! I used the Space Shooter Redux sprites, available here. Mainly just a project I used to practice JavaScript, specifically OO JavaScript using the base.js library. Coming from nice OO…
-
PiDoor – Security Door Lock v2
Some readers may recall my old security door lock, which I made about a year ago. It was controlled with just a single AVR, which proved very inflexible. Though in theory it was capable, it was very limited unless I spent a lot of time and effort interfacing with an internet connectivity module. While that…
-
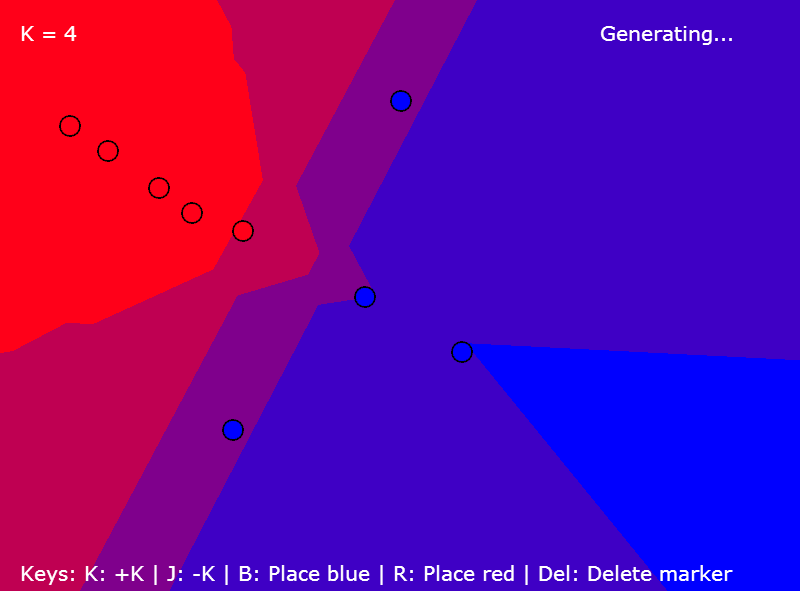
K-Nearest Neighbours
I spent a few hours over the past few days working on an interactive K-NN (K-Nearest Neighbours) classification map. Try it out here: http://projects.bitnode.co.uk/KNN/ If you’re unfamiliar with it, K-NN is a part of machine learning. Specifically, it can be used for classification (I.E does this belong to x or does it belong to y).…
-
DriveEditor – Vehicle config editor for BeamNG Drive
Another desktop application! This one was actually challenging, (which makes a change from other desktop applications I’ve made) and I learned a lot while creating a useful tool at the same time! Well, useful if you like smashing cars in BeamNG’s Drive: a softbody car physics simulator which is much more fun than it sounds!…
-
Radial Spatial Hashing for 2D Lighting
This builds on my previous system, which you can see in my previous post. If you want to learn how to make simple 2D lighting, read that first. If you want to know how to make it 10x+ faster, read this! So, this post deals with the issues faced with the inefficient method described originally…
-
Basic 2D Shadows and Lighting System (OpenGL, C#)
I’ve decided to tackle the challenge of 2D shadows and lighting first in my to-be 2D game. It’s something I’ve wanted to try for a long time, and never really had the guts to try. It seems like a daunting task, but after a few days of work, I’ve produced a basic lighting system which…